Using Audio to Verify the Integrity of 3D Printed Objects
 3D printing carries with it a host of security concerns. Tampering with a 3D printed object can happen remotely if someone hacks into the 3D printer while online, and no one may ever be any the wiser – until the component fails. It can be hard to verify the integrity of a 3D printed object by sight, so it takes some creativity to be able to determine that a part has not been tampered with. In a newly published paper, a group of researchers detail their method of verifying a 3D printing object’s integrity – via audio signature.
3D printing carries with it a host of security concerns. Tampering with a 3D printed object can happen remotely if someone hacks into the 3D printer while online, and no one may ever be any the wiser – until the component fails. It can be hard to verify the integrity of a 3D printed object by sight, so it takes some creativity to be able to determine that a part has not been tampered with. In a newly published paper, a group of researchers detail their method of verifying a 3D printing object’s integrity – via audio signature.
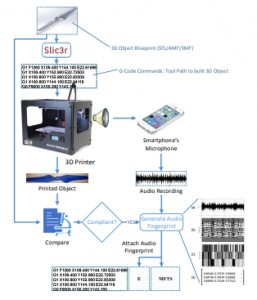
The paper, entitled “Digital Audio Signature for 3D Printing Integrity,” can be accessed here. In it, the researchers describe their tactic, which involves the acoustic side-channel emanations generated by the 3D printer’s stepper motors. Two algorithms are used to create a verification system. The first is used to generate a master “audio fingerprint” for the unaltered 3D printing process. The second is applied when the same object is 3D printed again, and it compares the audio produced during the printing process to the master fingerprint.
To evaluate the quality of the proposed thresholds, we identify the detectability thresholds for the following minimal tampering primitives: insertion, deletion, replacement, and modification of a single tool path command,” the researchers explain. “By detecting the deviation at the time of occurrence, we can stop the printing process for compromised objects, thus saving time and preventing material waste.”
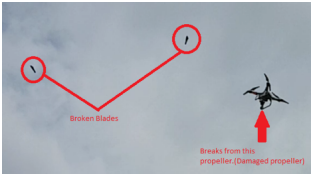 The researchers who completed this study are the same who deliberately sabotaged a 3D printed drone during the printing process in order to demonstrate how disastrous such tampering can be – and how easy it is to do, and difficult to detect. A phishing attack downloaded and replaced the files for a 3D printed replacement rotor blade, adding hollow cavities inside it that were invisible once 3D printed. The team 3D printed and attached the blade to a drone, which they then flew. Once the drone reached a certain height, the blade broke off, crashing the whole thing.
The researchers who completed this study are the same who deliberately sabotaged a 3D printed drone during the printing process in order to demonstrate how disastrous such tampering can be – and how easy it is to do, and difficult to detect. A phishing attack downloaded and replaced the files for a 3D printed replacement rotor blade, adding hollow cavities inside it that were invisible once 3D printed. The team 3D printed and attached the blade to a drone, which they then flew. Once the drone reached a certain height, the blade broke off, crashing the whole thing.
“Although this sabotage only led to the loss of a $1000 drone, similar attacks on functional parts for safety-critical systems may cause tremendous monetary losses, disruptions, and loss of human life,” the researchers point out.
The new study doesn’t use any specialized equipment, instead relying on a smartphone to record the sounds produced by the 3D print in process. The verification algorithm is implemented as a cloud-based app. The method can detect deviations of individual gcode commands, alerting users to even the smallest alteration in the design file.
The paper goes on to describe how the researchers tested their method several times, using a BCN3D Sigma 3D printer. There were a few challenges to the process, such as channel mismatch, which involved the recordings being mismatched thanks to other reasons than sabotage. These included background noise, different recording positions, different recording devices, and elapsed time from the recording of the master file. With careful attention, these issues can be overcome, and the researchers explain that the algorithm is designed to overcome a certain amount of background noise.
It’s incredible that smartphones are capable of such high-quality recording, which has a negative side as well – other scientists have pointed out that it’s possible for hackers to record the sounds a 3D printer makes while printing and then use those sounds to reverse engineer and reproduce an item. It’s a constant battle between hackers and those trying to prevent hacking, with each side armed with increasingly sophisticated tools. This latest study demonstrates an excellent way to verify the integrity of a 3D printed object, however, ensuring that critical components won’t be compromised.
Authors of the paper include Sofia Belikovetsky, Yosef Solewicz, Mark Yampolskiy, Jinghui Toh, and Yuval Elovici.
Discuss this and other 3D printing topics at 3DPrintBoard.com or share your thoughts below.
Subscribe to Our Email Newsletter
Stay up-to-date on all the latest news from the 3D printing industry and receive information and offers from third party vendors.
Print Services
Upload your 3D Models and get them printed quickly and efficiently.
You May Also Like
3D Printing Financials: Velo3D Revenue Up Fueled by Defense Momentum
Velo3D (Nasdaq: VELO) reported a strong start to 2026, with revenue rising as defense and aerospace customers continued shifting from pilot programs into full-scale additive manufacturing (AM) production. The company...
AMS 2027: The AM Industry’s Biggest Business Conversations Return to New York
Additive Manufacturing Strategies (AMS) is heading back to New York next February for what has become one of the industry’s most important business gatherings. The 10th annual AMS conference (or...
AM & the Military’s Self-Infliction of Rapid Change
I’ve noted before that the additive manufacturing (AM) market for defense has started to evolve so quickly that it’s impossible to even keep track of all the updates in real...
ROBOZE Buys Dimanex Assets to Build “Physical AI” Platform
Dutch firm Dimanex got its start as an MRO platform for the railways. The company had a contract with the Dutch Army in 2018, and later that year signed one...