More to Worry About: IP Thieves Could Use Smartphones to Steal Design Data from Your 3D Printer in Action!
 3D printing and the impacts it offers up to the world can be appreciated from numerous angles, meaning something very different for many, whether hobbyists or industrial operators, all with specific needs from making lightweight bicycle parts to manufacturing luxury vehicle components, or from creating new drone parts in a home workshop to making rocket engines at NASA. Originally meant as a tool so that engineers could easily create prototypes, this relatively simple technology is quickly becoming much more complicated, whether we like it or not.
3D printing and the impacts it offers up to the world can be appreciated from numerous angles, meaning something very different for many, whether hobbyists or industrial operators, all with specific needs from making lightweight bicycle parts to manufacturing luxury vehicle components, or from creating new drone parts in a home workshop to making rocket engines at NASA. Originally meant as a tool so that engineers could easily create prototypes, this relatively simple technology is quickly becoming much more complicated, whether we like it or not.
And while we certainly all enjoy seeing the emergence of new hardware and software that offers us more options at prices that just continue to go lower, as 3D printing increases exponentially in popularity, so do some of the headaches that no one really wants to have to deal with such as copyrighting and intellectual property issues, environmental and health/safety questions and concerns, and considerations for security that just seem to keep growing.
The topic of 3D printing and danger from malicious hacking is not new, and we’ve reported on the threat again just recently, in terms of potential vulnerability for cyberhacking shown during 3D printing orientation. Now, researchers from University at Buffalo are exploring just how easy it would be to hack into a 3D printer while it is in action, quickly stealing what could be valuable designs.
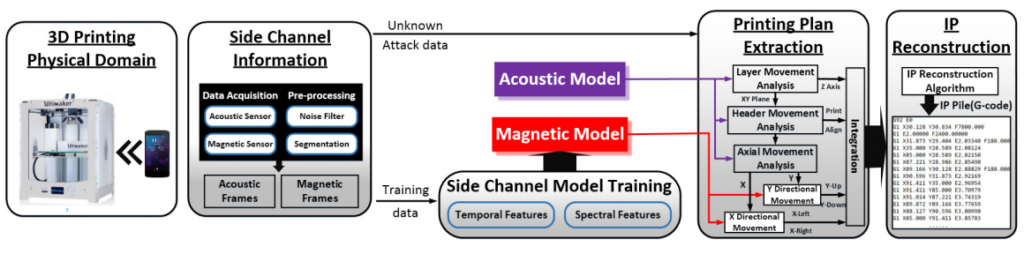
Outlining their findings in ‘My Smartphone Knows What You Print: Exploring Smartphone-based Side-channel Attacks Against 3D Printers,’ authored by Chen Song, Feng Lin, Zongjie Ba, Kui Ren, Chi Zhou, and Wenyao Xu, the researchers explain that intellectual property protection needs to be more strongly considered, and they show exactly why with evidence that smartphones can fairly easily hack other hardware like a 3D printer; in fact, they consider smartphones ‘ideal’ for stealing 3D intellectual property.
“Many companies are betting on 3D printing to revolutionize their businesses, but there are still security unknowns associated with these machines that leave intellectual property vulnerable,” said Wenyao Xu, PhD, assistant professor in UB’s Department of Computer Science and Engineering, and the study’s lead author.
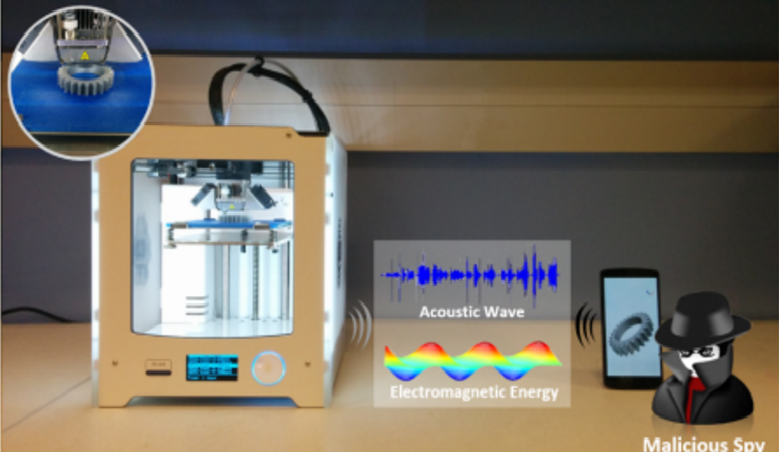
And while you might expect that for this study the researchers went to great lengths to strategize and then attack like traditional cyberterrorists, their exploration into IP theft from 3D printers was alarmingly simple. Indeed, working from their phones, they programmed the built-in sensors there to take measurements from electromagnetic energy and acoustic waves coming from a nearby 3D printer. They discovered that the sensors were able to pinpoint what the 3D printer nozzle was doing, tracking its movements—and thereby gaining access to the design and print. And while this may not be important if you are just making a logoed keychain or something small for the home, it is quite concerning for the number of high-security designs being made today—as well as more middle-of-the-road innovations that designers wish to protect as well.
Somewhat like the extremely high-tech, modern version of listening in on your phone call, your printer nozzle can be hacked, gleaning enough information for the IP thief to make exactly what you are at a 94 percent accuracy rate (this was however, from a distance of only 20 cm).“Smartphones are so common that industries may let their guard down, thus creating a situation where intellectual property is ripe for theft,” says Chi Zhou, PhD, assistant professor in UB’s Department of Industrial and Systems Engineering, another study co-author.
This is both scary and fascinating at the same time, considering certainly few of us had ever imagined something like this was possible in terms of side-channel access—and with such a ubiquitous tool.
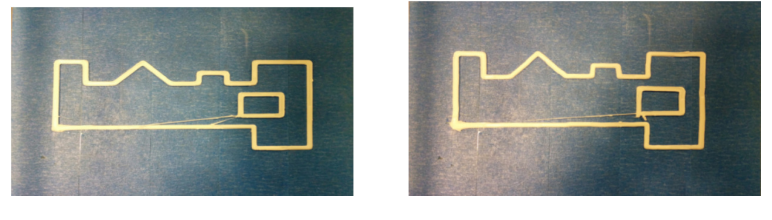
On the left is the original complex shape, and on the right is a replicated shape created after the smoothed reconstruction result.
“The tests show that smartphones are quite capable of retrieving enough data to put sensitive information at risk,” says Kui Ren, PhD, professor in UB’s Department of Computer Science and Engineering, a co-author of the study.
Explaining that the phones not only offer a ‘rich set of onboard sensors’ to work with, the researchers point out that their utter daily presence and compact size make them the perfectly inconspicuous hacking weapon. The research team offered a scenario in their paper:
“After entering the space where the 3D printer [is located], the attacker places the smartphone near the printer to collect side-channel information. Note that the smartphone does not need any physical contact with the printer. This is completely unsuspicious due to the pervasiveness of the smartphone nowadays and it is normal for people to place their smartphones on the table. With the recording application running on the smartphone, the attacker does not even need to be at scene. During the printing process, the smartphone records the side channel data simultaneously. Once the printing process is finished, the attacker fetches the smartphone and obtains the side-channel data…”
It’s certainly easy enough afterward to pick up the phone and go, and then get to work on attacking the printer status and function, using an IP conversion function to gain access to the data, and perform either a partial or complete attack. In performing their research, the team investigated elements such as:
- Distance and how it affects accuracy of an attack
- Print speed and how it could fend off accuracy of an attack
- Position affect and related acoustic signals
- Ambient noise and how it interferes with an attack
- The feasibility of carry-on attacks (where the individual hides a phone in their pocket, for example)
- How complex shapes being 3D printed affects data captured
They also recommend numerous ways to prevent such IP attacks to a 3D printer, such as the obvious distance or speed, as well as using dynamic printing configurations while generating G-Code.
“For example, the printing speed for a specific material has a proper speed range based on the material’s characteristic,” state the researchers in their paper. “Applying different speed settings within the proper range in the printing process will maintain the yield but reduce the attack accuracy. Different temperature settings in the nozzle heater are also be required to match the printing speed and will further generate additional interference in the side channels.”
The use of ‘dummy tasks’ is also suggested as they could fool smartphone sensors trying to detect data.
“Specifically, the dummy task comprises a set of random trajectories with the regular print speed yet no real material extrusion,” stated the research team. “The dummy task can be integrated in the process of G-Code generation. This defense approach can increase the print duration while have little impact on the print quality.”
As far as hardware, the team recommends both hardware shielding, as well as side-channel interference. Explaining that there is available electromagnetic shielding hardware that is effective, the researchers also point out that this route can be cost-prohibitive as additional equipment must be purchased and 3D printing operations may be affected too. For side-channel interference, a counter-attack on smartphone sensors can be launched with electromagnetic interference, as well as the possibility of noise functioning as suitable interference too. So far, the researchers are not sure about health concerns with this method though.
As we examine all of the angles from which security is an issue in 3D printing, studies such as these certainly offer important information as to how companies and individuals should be considering protecting their work. Whether someone is truly trying to steal valuable secrets, or whether an employee or acquaintance is considering sabotage, it seems all too easy to gain access to designs that may not be for public consumption.
“In the era of smart devices and internet of things, physical domain attacks leveraging cost-efficient and ubiquitous sensors deserve more attentions,” concluded the research team.
The researchers will present their findings at the Association for Computing Machinery’s 23rd annual Conference on Computer and Communications Security in October in Austria. Would you like a copy of the paper sent to you? If so, please contact Cory Nealon, university communications, at cmnealon@buffalo.edu. What are your thoughts on this information? Discuss further in the Hacking 3D Printers with Smartphones forum over at 3DPB.com.
[Source/Images: University at Buffalo]Subscribe to Our Email Newsletter
Stay up-to-date on all the latest news from the 3D printing industry and receive information and offers from third party vendors.
Print Services
Upload your 3D Models and get them printed quickly and efficiently.
You May Also Like
3D Printing News Briefs, May 3, 2025: Executives, Awards, & a 3D Printing Factory
We’re focusing on additive manufacturing business news today, as both Velo3D and PostProcess Technologies announced changes to their Boards of Directors. Sandvik Metal Powder has a new president, and Klas...
EOS Releases Medical Device Master File for M290 3D Printer
Laser powder bed fusion (LPBF) firm EOS has released a Medical Device Master File that will make it easier for customers to achieve regulatory success. The file will essentially be...
Velo3D Secures $22M Metal 3D Printing Powder Supply Deal with Amaero
Velo3D (OTCMKTS: VLDX) has signed a major new agreement with metal 3D printing powder manufacturer Amaero (ASX: 3DA). The five-year deal is valued at USD $22 million and centers around...
Push Button Metal 3D Printing for $50,000?
In 2021 we wrote an article about “Push Button Metal, the low cost metal 3D printing evolution we are not talking about.” In it, we talked about One Click Metal,...