Is nothing safe anymore? One could argue that nothing ever has been, really, but it’s a disturbing reality that in today’s technological world, in which almost everything is linked in some way to the Internet, security is continually being threatened in new ways. When 3D printing was in its early days, it’s likely no one ever imagined it could be a security threat, but the technology has definitely turned out to have a nefarious side – and I’m not just talking about 3D printed guns or copied keys.
Experts have warned that cybersecurity issues should not be underestimated when it comes to 3D printers, which, like anything else with a web connection, are potentially vulnerable to hacking. We may not hear about hacked 3D printers very often, but the potential is there, and researchers have been spending a lot of time trying to anticipate the worst. While on the surface, cyberattacks on 3D printers may seem like a relatively minor threat, with the most dire consequences being stolen intellectual property, the issue becomes a lot more serious when you start thinking about what 3D printers are creating nowadays. Airplane parts, rocket engines, even medical devices – if these things can be tampered with remotely, it’s not good, to say the least.
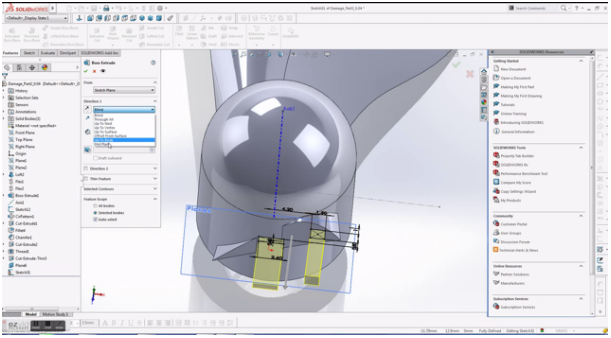
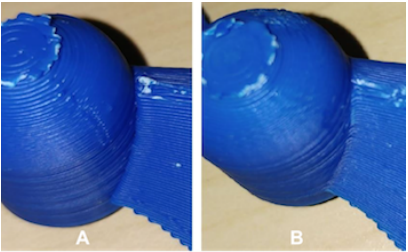
A team of professors from the University of South Alabama, Ben-Gurion University of the Negev, and Singapore University of Technology and Design recently carried out an experimental cyberattack on a partially 3D printed drone to demonstrate the damage that 3D printer hackers could potentially cause. The team orchestrated a phishing attack on the computer containing the files for a DJI drone. Once they accessed the computer, they downloaded the 3D file for a replacement rotor blade and added hollow cavities in the interior of the blade, weakening it in a way that wouldn’t be detectable by visual inspection.
According to Ben-Gurion University professor Yuval Elovici, the team deliberately engineered the design flaws so that they wouldn’t cause the propeller to fail right away, giving the drone enough time to get high into the air before breaking for maximum damage when it hit the ground. Once they printed the blade and attached it to the drone, they carried out a flight test, which went exactly as they had intended it to go; the drone flew normally for a few minutes before the sabotaged propeller blade flew off and sent the $1,000 drone crashing to the ground.
Full details of the research project were documented in a paper entitled “dr0wned – Cyber-Physical Attack with Additive Manufacturing,” co-authored by Elovici, Sofia Belikovetsky, Mark Yampolskiy, and Jinghui Toh. The researchers put together a video detailing their process and the intentionally failed flight, linked in the paper:
https://youtu.be/993h0rXP2P8
“Initially we focused on checking whether the 3D-printer can be hacked,” said Elovici. “Quickly, we realized that such an attack cannot scale due to the huge variety of 3D printers, and thus we decided to focus on how attackers may intervene in a generic way in the process between design and production.”
The paper breaks down multiple scenarios for how 3D printed parts could be compromised, and the large number of feasible methods is unsettling. Although a widespread cyberattack on multiple 3D printers is unlikely, Elovici said, plenty of damage can still be done by manipulating one single part.
“Imagine that an adversary can sabotage functional parts employed in an airplane’s jet engines,” he said. “Such an attack could cost lives, cause economic loss, disrupt industry, and threaten a country’s national security.”
While the research team’s attack was targeted at a private personal computer, they warned that a similar attack could be carried out on an industrial or corporate computer system, which has the potential to cause a lot more problems. It’s a grim realization, but the intent of the study wasn’t to scare people but rather impress upon them the need for strict security measures in additive manufacturing facilities.
“…[B]efore printing an object, there is a need to check that the file was not modified and there are many cryptographic means that can be used in order to achieve this goal,” Elovici said. “The research community is currently engaged in developing innovative methods that involve innovative data verification techniques that verify that what is printed is exactly [the] content of the original design.”
Discuss in the Drone Sabotage forum at 3DPB.com.
[Sources: dr0wned – Cyber-Physical Attack with Additive Manufacturing; EurekAlert; TechRepublic]Subscribe to Our Email Newsletter
Stay up-to-date on all the latest news from the 3D printing industry and receive information and offers from third party vendors.
You May Also Like
Gorilla Sports GE’s First 3D Printed Titanium Cast
How do you help a gorilla with a broken arm? Sounds like the start of a bad joke a zookeeper might tell, but it’s an actual dilemma recently faced by...
Nylon 3D Printed Parts Made More Functional with Coatings & Colors
Parts 3D printed from polyamide (PA, Nylon) 12 using powder bed fusion (PBF) are a mainstay in the additive manufacturing (AM) industry. While post-finishing processes have improved the porosity of...
$25M to Back Sintavia’s Largest Expansion of Metal 3D Printing Capacity Since 2019
Sintavia, the digital manufacturing company specializing in mission-critical parts for strategic sectors, announced a $25 million investment to increase its production capacity, the largest expansion to its operations since 2019....
Velo3D Initiates Public Offering in a Bid to Strengthen Financial Foundations and Drive Future Growth
Velo3D (NYSE: VLD) has been among a number of publicly traded 3D printing firms that have attempted to weather the current macroeconomic climate. After posting a challenging financial report for 2023,...