Keysforge: Easy, Automatic Production of 3D Printed Copies of High-Security Keys
 While retinal and other biometric scanners are coming into play for some high-security applications, there’s still some ways to go before those are reliable enough for more common use–and so most secured areas rely on the age-old standby of the lock and key. The idea, of course, behind a lock is that it can only be opened by the correct key. As any teenage girl who had a diary with a plastic lock can tell you, though, locks can be picked (I’m looking at you, big sister who broke into my middle school journals). The art of lock picking is about as old as the lock itself.
While retinal and other biometric scanners are coming into play for some high-security applications, there’s still some ways to go before those are reliable enough for more common use–and so most secured areas rely on the age-old standby of the lock and key. The idea, of course, behind a lock is that it can only be opened by the correct key. As any teenage girl who had a diary with a plastic lock can tell you, though, locks can be picked (I’m looking at you, big sister who broke into my middle school journals). The art of lock picking is about as old as the lock itself.
 As technology advances, so does its counterpart; in this case, that means that as security measures have become higher-tech, so have the means to bypass them. With 3D scanning and printing technology becoming not just more precise, but more accessible, those seeking entry into theoretically unpassable areas are increasingly able to simply make their own keys. From learning how locks work for the casually curious to thwarting scanning measures with the Stealth Key that hides its mechanisms internally, 3D technologies allow for a thorough look into locking and lock picking.
As technology advances, so does its counterpart; in this case, that means that as security measures have become higher-tech, so have the means to bypass them. With 3D scanning and printing technology becoming not just more precise, but more accessible, those seeking entry into theoretically unpassable areas are increasingly able to simply make their own keys. From learning how locks work for the casually curious to thwarting scanning measures with the Stealth Key that hides its mechanisms internally, 3D technologies allow for a thorough look into locking and lock picking.
While in 2013, MIT students had demonstrated that this technology could be used to duplicate keys that were meant to be non-replicable, they did not release their software, as it was more a study in plausibility than a practical effort. Last year, bump key technology from Jos Weyers and Christian Holler led to a heightened awareness that 3D scanning could lead to accurate recreations of keys that could then be 3D printed, bypassing security measures.
New research coming now out of the University of Michigan takes these concepts and acts on them. Not only has the team developed a way to replicate security keys, but Ben Burgess, Eric Wustrow, and J. Alex Halderman released their findings yesterday in a full paper and a usable app.
Their paper, ‘Replication Prohibited: Attacking Restricted Keyways with 3D Printing,’ provides an in-depth look at the thoughts and theories behind their Keysforge app.
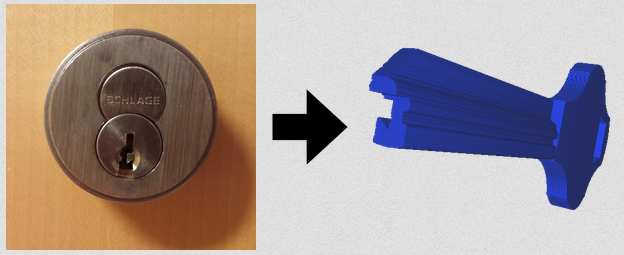
“This website demonstrates a tool that generates a CAD model of a key blank from a single picture of a lock. This model can then be 3D printed cheaply in either plastic or metal from a number of services,” notes the Keysforge site.
“Such a tool can be used to get around restricted keyways, a defense currently employed by locksmiths and designers to prevent a wide range of attacks including bumping, impressioning, privilege escalation, and teleduplication.”
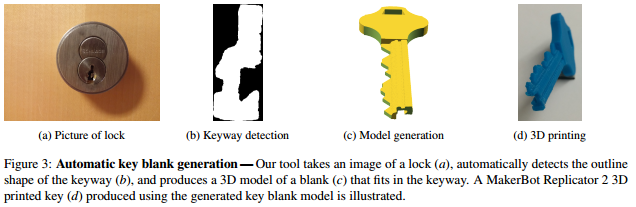 The idea behind the keys that manufacturers offer for high-security applications is that a patented ‘blank’ template will be released to only their clients. Using the Keysforge app, however, all that is needed is an image of the key to be duplicated and a straight-on photograph of the lock it opens; the software does the rest.
The idea behind the keys that manufacturers offer for high-security applications is that a patented ‘blank’ template will be released to only their clients. Using the Keysforge app, however, all that is needed is an image of the key to be duplicated and a straight-on photograph of the lock it opens; the software does the rest.
Of course, 3D printing offers its own limitations, as most familiar with the technology know. Keys are typically made of metal, and 3D printing metal is still inaccessible for desktop 3D printers. The Keysforge team turned to several different types of 3D printers and materials in their proof-of-concept work.
“To evaluate the viability of using both metal and plastic 3D printed keys in attacks against restricted key systems, we produced several designs of keys, had them printed in several materials, and measured how much torque they could withstand before breaking,” the researchers describe in their paper. “We chose three common keyways: SC1, KW1, and Best G. For each keyway, we created a 3D model using OpenSCAD (a 3D modeling suite), with random cuts on the keys. After prototyping these models using a MakerBot Replicator 2, we contacted a 3D printing service to fabricate them in several materials including nylon plastic, acrylic plastic, alumide plastic, brass, bronze, and stainless steel.”
The team’s findings showed that, somewhat surprisingly, PLA material printed using a desktop MakerBot 3D printer produced a key that held up significantly better than did more costly nylon and acrylic. While the plastics were, unsurprisingly, not exactly ideal for keys, the team had better luck with stainless steel, printed through Shapeways and i.materialise services–though these keys had a tendency to damage the locks. Below is a look at the team’s findings regarding material strength from their paper.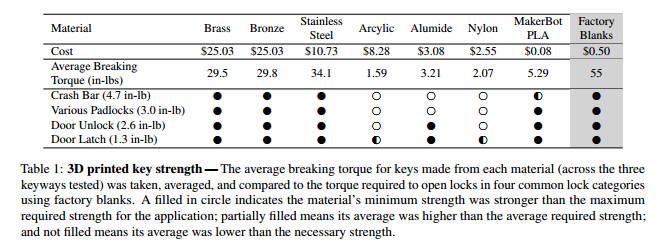
Keysforge is intended to provide information to those in the lock industry, not as a tool for thieves. Just as the FBI and other bureaus focusing on matters of safety and security employ their own hackers set to discover any potential weaknesses in a system, Keysforge is a tool that its makers believe will serve to raise awareness among lock and key manufacturers as well as the general public about “just how inexpensive these attacks are with modern tools. In addition, allowing a larger audience to use the tool may help defenders discover particular features of keyways that make them difficult to produce with this method, further assisting lock designers that want to defend against this technology.”
Research from Keysforge was published in the Proceedings of the 9th USENIX Workshop on Offensive Technologies (WOOT), August 2015, and will be presented next week in an in-depth presentation at WOOT ’15 in Washington, D.C. The team provides the source code on GitHub. Let us know your thoughts on the latest in key security in the 3D Printed Keysforge forum thread over at 3DPB.com.
Subscribe to Our Email Newsletter
Stay up-to-date on all the latest news from the 3D printing industry and receive information and offers from third party vendors.
Print Services
Upload your 3D Models and get them printed quickly and efficiently.
You May Also Like
AM Asia Watch: China’s HeyGears Lands $44M to Expand Beyond Dental 3D Printing
Chinese 3D printing company HeyGears raised more than 300 million Yuan (roughly $44 million) in a new Series C funding round as it looks to expand beyond its industrial and...
The University of Utrecht: “3D Printing Could Change Who Gets to Become a Manufacturing Power”
For decades, manufacturing has mostly been controlled by countries with huge factories, lower labor costs, and industrial systems that took years, sometimes decades, to build. But Utrecht University human geographers...
3D Printing News Briefs, May 28, 2026: Continuous Fiber Reinforcement, Bioprinted Trachea, & More
In today’s 3D Printing News Briefs, America Makes announced the winners of its JAQS-SQ Project Call. Axtra3D is partnering with Keystone Industries to expand its dental material ecosystem, while BigRep...
Asia AM Watch: China’s SHINING 3D Restarts IPO Review Process
SHINING 3D is moving forward again with its plans to go public in China, after restarting its Beijing Stock Exchange (BSE) initial public offering (IPO) review process and filing updated...