TSA-Approved Master Luggage Keys Hacked and 3D Printed Once Again
Last year, the Transportation Security Administration (TSA) found themselves in a bit of an awkward situation when they proudly posted photos of their new master luggage keys, only to have them promptly digitized and 3D printed by some clever hackers (who also posted the files online). The master keys were provided by a company called Travel Sentry, one of two TSA-approved lock companies. The other, Safe Skies, was apparently good as far as their master key security went – until now.
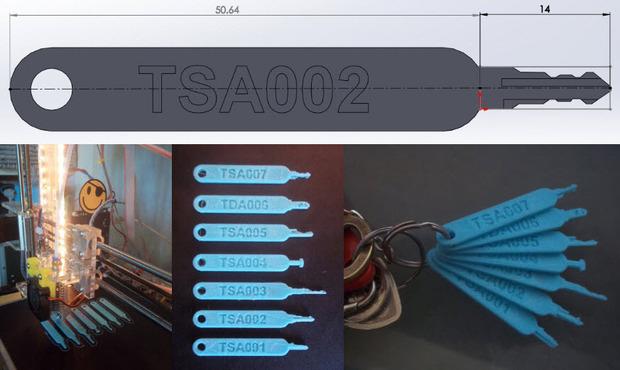
On Saturday, at the Eleventh annual HOPE (Hackers On Planet Earth) conference in New York, three hackers who go by the code names DarkSim905, Nite 0wl and Johnny Xmas unveiled a 3D printable model of the Safe Skies TSA master key. This time, the process was a bit more complicated, as no photos of the keys had been published online, but for an experienced hacker, that wasn’t a problem – it just slowed things down a little.
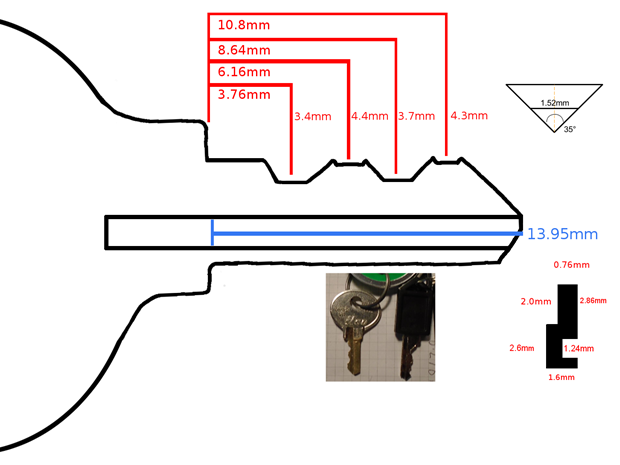
Nite 0wl, who, along with Johnny Xmas, was part of the Travel Sentry hack in 2015, started by buying Safe Skies locks from as many different locations as possible so that he had a good-sized sample to work with. He then began modifying commercially available key blanks to resemble the keys provided with the locks he had bought – not matching them exactly, as obviously Safe Skies wouldn’t release consumer keys that matched their TSA locks. He was able to eliminate the cut patterns on the keys he had purchased, while still using them to ascertain the general type of pattern Safe Skies uses, and thus, roughly, what a master key might look like.
With some additional tweaking and fine-tuning, Nite 0wl and his fellow hackers were able to come up with a 3D model of a key capable of opening Safe Skies’ TSA locks. It’s interesting to note that while that key is now 3D printable, 3D technology wasn’t used in the actual hacking process – only manual examination, trial and error, and a lot of time.“The big breakthrough was when I acquired several Safe Skies locks that used wafer-tumbler mechanisms instead of pin-tumbler mechanisms, because of the different mechanical design I was able to work out the master key cuts very quickly and then confirm that the key worked on all of the sample locks I had,” he told CSO.
It’s an unsettling metaphor, for sure, and a reminder that nothing is ever completely secure – on or offline. The hackers have stated that the purpose of the project was not to scare people with the idea that anyone can use a 3D printed key to break into their luggage – and that wasn’t their goal in releasing the files for the Travel Sentry keys, either. The point, which they say was completely missed in 2015, was to highlight the dangers of government key escrow, a data security measure in which a third party is trusted with a cryptographic key that they may only use with the authorization of the entrusting agency.“This was done by legally procuring actual locks, comparing the inner workings, and finding the common denominator. It’s a great metaphor for how weak encryption mechanisms are broken – gather enough data, find the pattern, then just ‘math’ out a universal key (or set of keys),” said Johnny Xmas. “What we’re doing here is literally cracking physical encryption, and I fear that metaphor isn’t going to be properly delivered to the public.”
The whole thing is interesting to think about, though – while 3D printing and other technology have brought with them a lot of anxiety about security, they’re not the only ways that security can be broken. Sure, the Travel Sentry keys were much easier to copy, but even without pictures that were ready to be turned into 3D models, the Safe Skies keys were eventually able to be hacked. It’s not a comforting thought, but it’s an interesting – and important – one. Let’s discuss this topic further over in the TSA Hacked Keys forum at 3DPB.com.
[Source: CSO]
Subscribe to Our Email Newsletter
Stay up-to-date on all the latest news from the 3D printing industry and receive information and offers from third party vendors.
Print Services
Upload your 3D Models and get them printed quickly and efficiently.
You May Also Like
First Containerized System from AML3D Now Operational at US Navy AM CoE
Shipbuilding giant Austal USA recently announced the launch of the Digital SEA (Secure Exchange for Additive) platform, which should play a major role in expanding accessibility to the sorts of...
3D Printing Financials: Materialise Improves Margins Despite Flat Revenue
Materialise (Euronext and NASDAQ: MTLS) started 2026 with stable revenue, stronger margins, and better operating profit, helped by growth in medical and improved profitability in software. The Belgian 3D printing...
3D Printing News Briefs: May 7, 2026: Metal Powder Bed Fusion, Surgical Plates, & More
In today’s 3D Printing News Briefs, we’ll start with a strategic collaboration to advance next-generation metal additive manufacturing (AM), before moving on to funding for surgical research. We’ll end with...
3D Printing News Briefs, May 2, 2026: Soft Robots, Agricultural Waste, & More
In this weekend’s 3D Printing News Briefs, we’ll start off with a multi-laser metal powder bed fusion 3D printer and post-processing news. We’ll end with research into soft robotics and...