DEFCON: Fooling Biometric Sensors Using 3D Printed Fake Fingerprints
Like most biometric identification systems, fingerprint locks provide adequate protection from malicious attacks, but they can be fooled by criminals to gain access to personal data hidden behind the fingerprint in smartphones or accounts. The use of biometric data for authentication is not new, face recognition, retina scanning, and voice identification are often used as substitutes for passwords. Several methods have been created to hack them, but in the last few years, 3D printing technology made it possible for anyone to create fake fingerprints and use them to gain unauthorized access to a system. At the DEFCON 2020 virtual security conference on August 8, Security Researcher at Dreamlab Technologies and 3D printing enthusiast Yamila Levalle described how she was able to bypass finger authentication using just a UV resin-based SLA 3D printer and $10 worth of materials.
Biometric systems are prone to different attacks, but Levalle chose to focus on spoofs, which happen when a sensor is fooled instead of being replaced or tampered with. According to the expert, to get a match, most fingerprint scanners use complex algorithms to recognize, measure, and analyze distinctive features, “similar to recognizing part of the sky through the relative position of the stars.” First, she chose to try out some traditional methods to bypass sensors, such as grease attacks using gummy bears and play-doh, to understand how 3D printing technology could make these attacks better and faster.
To test the attacks using 3D printing, Levalle used an Anycubic Photon 3D DLP/SLA printer she had at home; UV resin; software to digitally enhance the latent fingerprint; a 3D CAD design tool, like Tinkercad, and a latent fingerprint in glass or a fingerprint ink in paper.
The in-depth how-to guide required to obtain a working fingerprint involved lifting the latent fingerprint with a digital camera that had macro functionality and then, used a digital enhancement tool, such as Python or any kind of graphic software, in order to optimize the lines. Once the enhanced JPG file is converted to an SVG (Scalable Vector Graphics) file it can be imported into Tinkercad, where the dimensions and ridge height are configured to create a 3D model of the fingerprint. This, Levalle claims, is the most important step, making sure that the fingerprint length and width are printed according to the measures of the original latent fingerprint because the correct ridge height will allow the fake fingerprints to work in different sensors and scanners. Human papillary ridges, in general, have a height between 20 and 60 microns, so for this particular research, the 25-micron precision of a UV resin-based device did the job.
Finally, Levalle recommended creating two different 3D models, one negative or hollow for casting and one positive for direct tests. Then it’s off to the 3D printer. Once the prints are done, they are rinsed in Isopropyl alcohol and post-cured using a UV lamp or direct sunlight. To cast the finger, the 3D printed hollow molds were filled with just a few drops of liquid latex or wood glue (claiming that thin fake fingers work better than thicker ones) and as it dried, it solidified to a rubbery consistency.
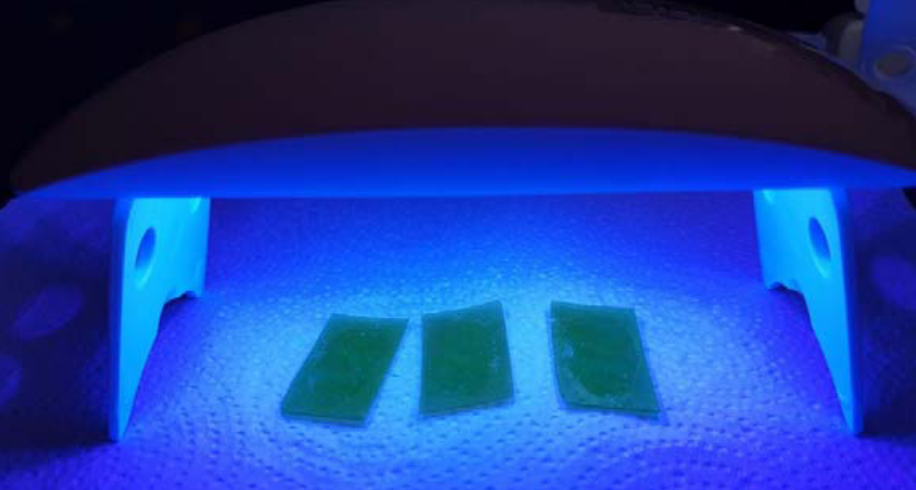
3D printed molds in the UV post-curing lamp. (Image courtesy of Dreamlab Technologies/Yamila Levalle)
It took Levalle ten tries to achieve the optimal printer settings and ridge height. Out of the two options she created, the fingerprint obtained from the 3D mold with liquid latex or wood glue casting worked on all four sensors, from the latest ultrasonic fingerprinting scanning technology used in Samsung S10 smartphones to the older optical fingerprint sensor models, although here she needed to spread cocoa butter lip balm or petrolatum over the fake fingerprint for the sensor to actually recognize it. On the other hand, the positive model 3D printed directly on UV resin only worked with the ultrasonic sensor and one of the opticals, mainly due to the hardness of the resin which failed to be recognized as a finger.
3DPrint.com virtually caught up with Levalle who said it took her half an hour to 3D print a lot of eight out of the ten fake fingerprints. “Determining the exact ridge height that would work to bypass the system took a few tests. Since I didn’t have an electronic microscope to measure the ridge height of the finger, I had to ballpark it based on the average ridge height of human fingers. There was quite a bit of trial and error until I got it right. What really helped here was the UV resin printer, this would not have been possible using an FDM or filament 3D printer since it does not have the same presicion,” she said.

Casting the 3D printed molds with liquid latex and wood glue. (Image courtesy of Dreamlab Technologies/Yamila Levalle)
The vulnerabilities with biometrics in smartphones, laptops, scanners, and other devices, usually attract security experts that have identified serious privacy concerns and ways in which criminals can breach these systems. For over 28 years, DEFCON, the world’s largest and oldest cybersecurity conference, has gathered both authorities and innovators in the cybersecurity space, offering an unparalleled perspective on the threats faced by emerging technologies and how to defend against them. For the first time ever, the 2020 conference has been put into “safe-mode,” as the in-person event expected to take place from August 6 through 9 has been canceled due to the ongoing COVID-19 pandemic.
Like with many DEFCON presentations in the past, hack instructions are extremely detailed and can be replicated by experienced security experts. In the past, attendees at DEFCON in Las Vegas were able to participate in dozens of presentations, from how-to-guides to hack 20 devices in 45 minutes, to incredible stories of hackers that targeted government systems (considered a must-watch for anyone in the hacker community considering a job with government agencies). Levalle’s presentation highlighted various vulnerabilities in a system that is dominating different markets, most of which seem to be growing rapidly. With 1.5 billion mobile users alone expected to rely on biometrics security by 2023 and nearly 60% of businesses using fingerprint scanning technology, it is clear that biometric authentication will only increase, and so will the threats.
“After going through several information leaks from biometric data companies, I felt motivated to do the work, and show the steps required to actually go through with an attack. At a cybersecurity competition in 2019, I witnessed a team that managed to hack fingerprint sensors, but there was not much information on how they did it, just that they took a photo of a fingerprint on a glass and then 20 minutes later, they had a fake fingerprint. So I tried to replicate this at home with my own device and chose to publish a white paper on it with my colleagues,” explained Levalle. “This is a great way to improve biometric security so that it can detect fake fingerprints used in spoofing attacks.”
In order to detect presentation attacks on fingerprint systems, Levalle and a team of researchers suggested analyzing the degree of sharpness, color, and luminance levels of the sample, entropy, structural distortions, local artifacts, light absorbance, material elasticity, and moisture content. But even as scanners and security experts become better equipped to detect falsified biometric data, cybercriminals will also be trying their best to create better fakes, and continue zeroing in on data theft.
You can watch the presentation here:
Subscribe to Our Email Newsletter
Stay up-to-date on all the latest news from the 3D printing industry and receive information and offers from third party vendors.
Print Services
Upload your 3D Models and get them printed quickly and efficiently.
You May Also Like
ROBOZE Buys Dimanex Assets to Build “Physical AI” Platform
Dutch firm Dimanex got its start as an MRO platform for the railways. The company had a contract with the Dutch Army in 2018, and later that year signed one...
3D Printing Financials: Nano Dimension Reports Q1 Growth Amid Restructuring and Asset Sales
Nano Dimension (Nasdaq: NNDM) started 2026 with a much larger first quarter business than it had a year ago, mainly because Markforged is now part of the company and included...
DMG Mori Joins $10M Defense 3D Printing Program
To look at the Biden administration and the Trump administration that succeeded it and find areas of policy overlap is obviously a bit of a challenge. But such areas certainly...
3D Printing & Drone Dominance: Speed, Performance, and Derisking the Supply Chain
A shift is underway in drone manufacturing. Government programs like the U.S. Department of War’s Drone Dominance, a $1.1 billion effort to deliver low-cost, one-way attack (OWA) sUAS at scale,...