Thesis Student Tests for CyberAttack Risks in Distributed 3D Printing
Charles Ellis Norwood recently presented a thesis, ‘Demonstration of Vulnerabilities in Globally Distributed Additive Manufacturing,’ to the Virginia Polytechnic Institute and State University.
Norwood explores new methods in transferring data for manufacturing, as 3D design files can be sent virtually anywhere—with the potential for being 3D printed in a faraway area of the world. While this offers great ease in delivery of data and potential products, such methods of communication also mean that the designer gives up control and in some cases protection of parts.
“Industrial parts are increasingly produced by additive manufacturing,” states Norwood. “Several studies have shown the potential for additive manufacturing to improve supply chains for spare parts. With advances in additive manufacturing and the rise of globally distributed manufacturing, the logical step is to combine the two into globally distributed additive manufacturing. In one potential model of this system, designers and manufacturers would be two different entities in different places in the world. A design firm could engineer and develop a product, then hire an independent manufacturer to produce it. Designers could have as much or as little manufacturing capability as they need, and manufacturers could function solely to produce parts.
“With such a system, the major advantages of globally distributed manufacturing are realized. If a consumer decides to purchase a product, the original design firm could find the manufacturer closest to the consumer and have it produced. With additive manufacturing, products can be produced on demand, so an ideal system could effectively eliminate the need to keep stocks of parts or products. Consequently, it would reduce all associated costs such as warehouses and logistics for part organization.”
Norwood focuses on security in such transmissions, and the need for encryption to avoid cyberattacks and the possibility of failure in critical 3D-printed parts due to malicious activity. The need to make sure security is offered within the technology is critical due to the lack of enforcement of intellectual property measures in other countries; for example, transmissions being exchanged from one US manufacturer to another are expected to be safe due to understanding of the laws and possible punishment due to any infractions. Other countries, however, are well-known for blatantly ignoring IP laws.
“There could be little legal recourse for international IP theft,” stated Norwood. “Rather than legal solutions, technological solutions could help protect IP when transmitted across international borders.”
Norwood assessed stepper motors and associated encrypted code in a simulated research study, seeking security flaws. While encryption is not always easily hacked these days, data becomes open to attack when the secure printer decrypts the code and changes it to instructions for printing.
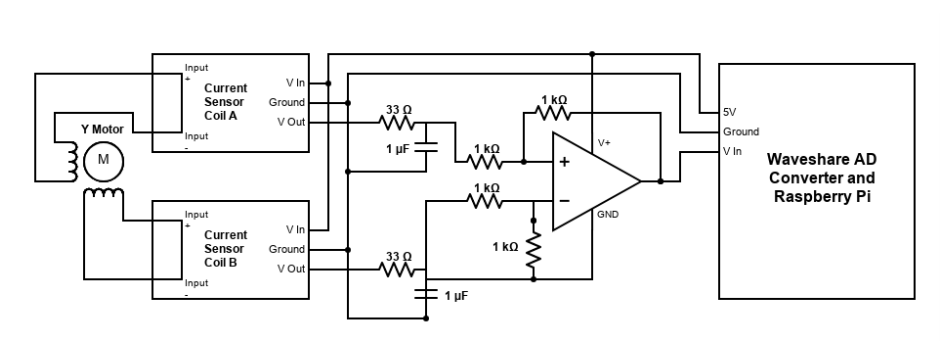
“The G-Code instructions control the paths of the motors, heaters, and other processes of the printer. Printer software converts the G- 4 Code to stepper motor control signals, which motor drivers use to operate the stepper motors. Motor drivers send power signals along wires to the stepper motors, which control the physical motion of the printer as it prints parts,” states Norwood.
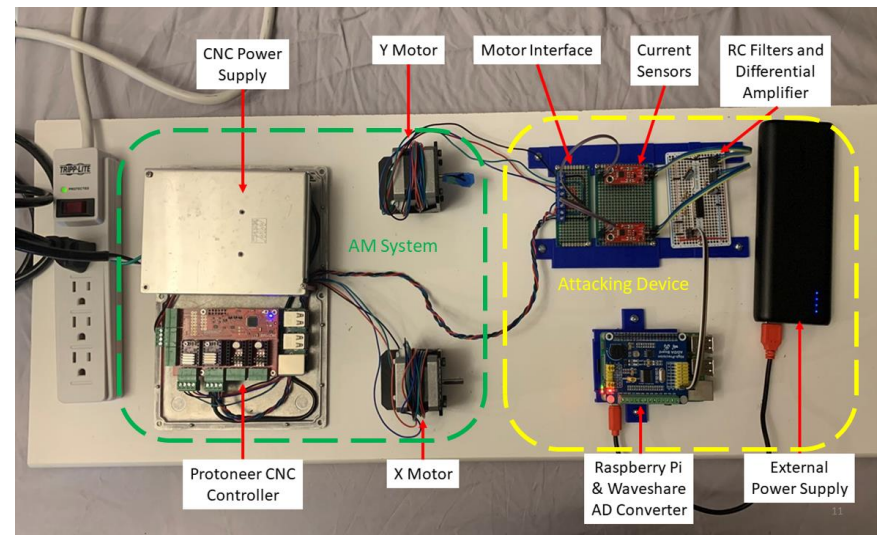
A hacker can feasibly detect all movements and pulse patterns, analyze them, and reverse engineer the process, resulting in their ability to rebuild stolen 3D-printed parts from their own end. And, while this type of attack sounds sophisticated, it is possible. For testing, Norwood used both a simulated additive manufacturing machine (consisting of the controlling computer, motor drivers, motors, and an external 24V power supply) and then an “attacking device” capable of translating the current transmitted through the motor wires—and then translating them (in reverse engineering mode) back into G-Code for use.
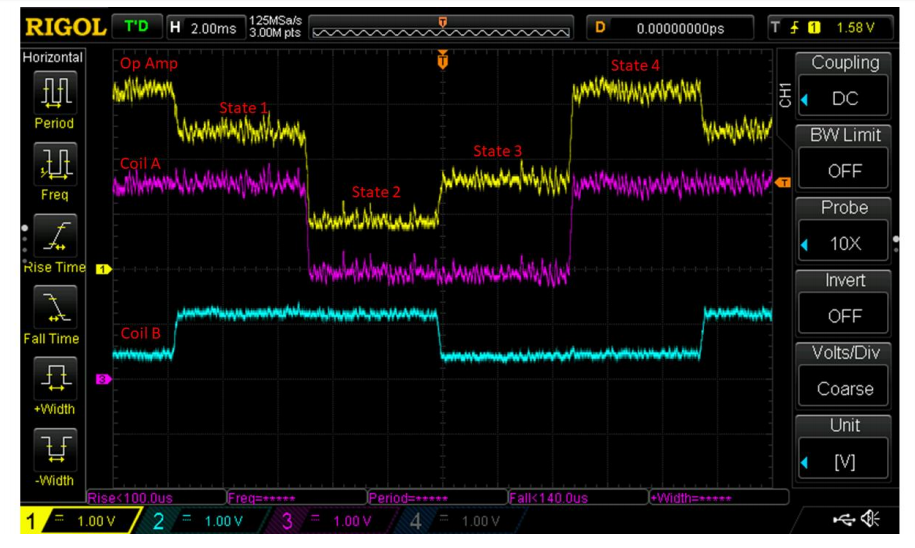
“The sequence of coil charging is controlled by the stepper motor driver. The “state” column refers to the state of the stepper motor. As the motor turns, it progresses through four distinct states depending on the voltage of the coils,” explained Norwood.
The author was able to create a range of tests based on the sensors, recorders, and processors for analysis of forward or reverse motor motion, along with copying G-Code instructions similar to what would be used for a 3D-printed part. Clarifying that although the method was not 100 percent successful (possibly due to errors caused by the 3D printing simulation), Norwood stated that the success rate in assessment was high enough to show that his method was effective for long data sequences. It is also important to note that he was able to run a basic attack in simulation with a customized system costing under $100.
“To perform a full system test, one would not need to perform significant research and development of the attacking system. The approach for one motor could be repeated for all other printer motors, the data synchronized, and a full G-Code program recovered. The techniques presented in this thesis merely need to be repeated on more precise, advanced equipment to demonstrate a full system attack,” concluded the author.
“A system is only secure when the costs to hack it exceed the financial benefit. More advanced sensors, data recorders, and processors would not be prohibitively expensive. Advanced technology intellectual property can be worth millions of dollars, so it must be protected.”
Malicious attacks within the 3D printing industry have occurred before, such as the crypto-mining attack on Thingiverse, and users are aware of cyber threats, prompting challenges like cybersecurity hackathons, and graduate courses educating students on cybersecurity in additive manufacturing.
Pointing out that any transmitted data—encrypted or not—presents vulnerability, the author mentions other suggested solutions for preventing theft or pirating:
- Fingerprinting or watermarking of products
- Tracking of the entire information flow
- “Smart contracts” ensuring security of data between entities working together
Subscribe to Our Email Newsletter
Stay up-to-date on all the latest news from the 3D printing industry and receive information and offers from third party vendors.
Print Services
Upload your 3D Models and get them printed quickly and efficiently.
You May Also Like
3D Printing News Briefs, May 30, 2026: RIMPAC 2026, Acquisition, Ceramic Implants, & More
We’re kicking things off with materials news in this weekend’s 3D Printing News Briefs. Then it’s on to a hybrid manufacturing system for a maritime exercise, an expansion of industrial...
The Hidden Cost of Lost Engineering Intent
Recent reporting on the UPS MD-11 engine separation on Flight 2976 has understandably focused on the immediate question: what happened? The investigation will determine that, as it should. Serious engineering...
Scientists Create Stretchy 3D Printed Implants for High Blood Pressure Treatment
Researchers at Pennsylvania State University (Penn State) say they may have found a softer, less invasive way to treat severe high blood pressure. In a new study published in the...
Conexeu Sciences Wishes to Make a Regenerative Breast Matrix Solution (and sell shares)
Conexeu Sciences wants to commercialize a regenerative breast matrix solution. For years, Australian firm BellaSeno and Lattice Medical have been working on similar solutions. In 2018, Lattice came out with...