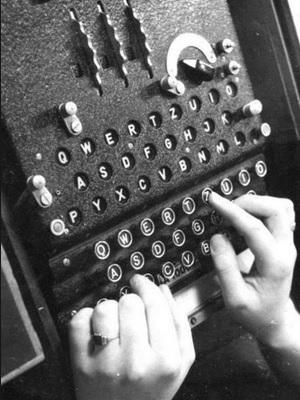
The Enigma machine was a decryption/encryption device most well-known for its use in World War II, when it was developed by the Germans and cracked by the British. Ultimately employed to decrypt crucial German messages, the Enigma is known to be a rarely found machine that may have actually been responsible for ending the war perhaps as much as two years ahead of time thanks to a crack team of code breakers including Alan Turing, as featured in the 2014 movie The Imitation Game. Code breaking was obviously an important duty during the war—and has been during many wars historically—and those who were able to do so were held in high esteem, along with their machines.
The Enigma machine was a decryption/encryption device most well-known for its use in World War II, when it was developed by the Germans and cracked by the British. Ultimately employed to decrypt crucial German messages, the Enigma is known to be a rarely found machine that may have actually been responsible for ending the war perhaps as much as two years ahead of time thanks to a crack team of code breakers including Alan Turing, as featured in the 2014 movie The Imitation Game. Code breaking was obviously an important duty during the war—and has been during many wars historically—and those who were able to do so were held in high esteem, along with their machines.
The German military was responsible for the manufacturing of the machine as early as the 1920s. With it, they began to encrypt messages due to a scrambling system powered by rotors and electronics. A message could not be figured out unless the settings of the rotors were known, and the Germans tried to stay ahead of everyone else, even adding another rotor. Although that war has faded into history and the machine is certainly obsolete at this point, it’s still a great source of fascination, and enough so, as Hackaday pointed out recently, that makers and hackers have shown interest in re-creating them, as well as making other projects that are related to the encryption machine.
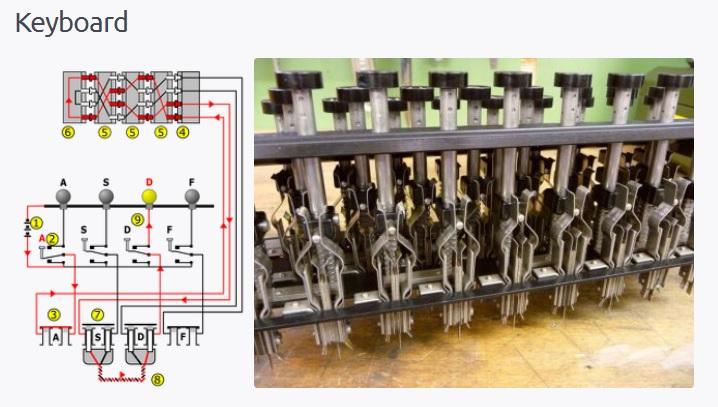
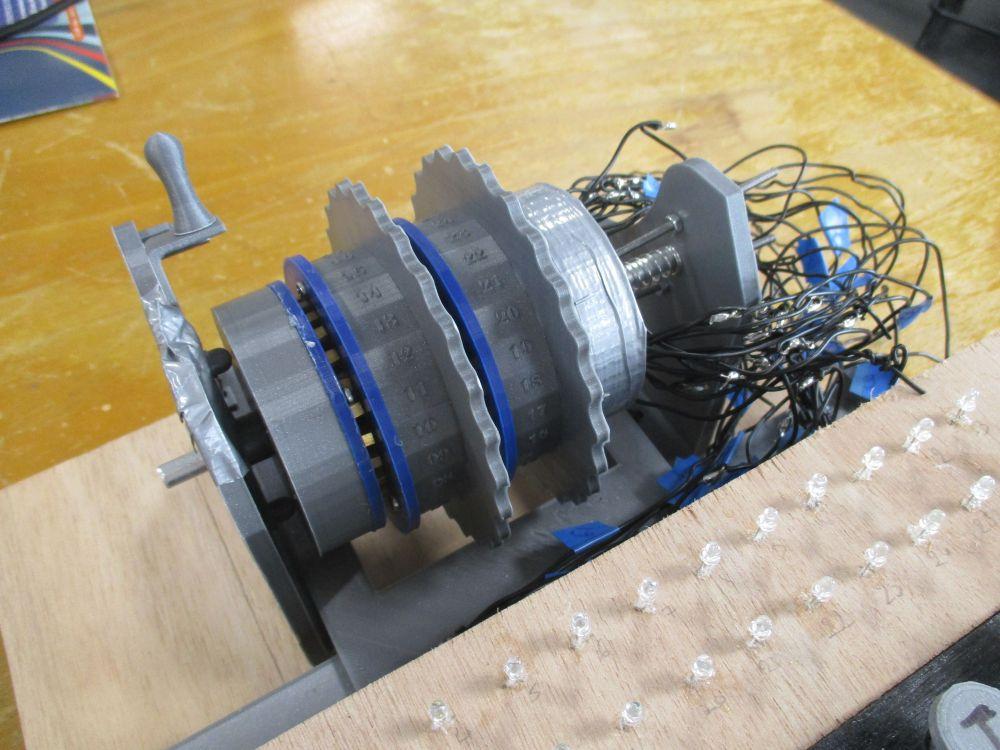
Now, we see the Enigma continuing on into posterity via a project from students studying in their first year at CentraleSupélec Rennes, in Northwestern France. First year or not, they’ve certainly shown their mechanical engineering chops with the Enigma, consisting of rotors that harken back to the design of the originals, yet showing off some high-tech flair with a 3D printed housing shell that holds brass contacts and the writing. Modern microswitches are also used for the keyboard although the students used an aesthetic design that is reminiscent of the original. They also added their own look with the AZERTY layout, using the French equivalent of the well-known QWERTY keyboard which was established for the traditional alphabetical layout meant to be used with typewriters.
The rotors are what make this 3D printed device unique, and as you can see in the explanation written by the students regarding the design, it has either three or four 3D printed rotors, along with the 3D printed compensator, that work to encrypt the letters. Both the keyboard and sub-keyboard were constructed out of wood. The keys were made by using an aluminum pipe that with a 3D printed touch at the top. They painted on the letters by hand, and then created the keyboard from several layers of wood, measuring at 5mm each. The team then glued them and drilled them together.
All of their 3D design was performed in SOLIDWORKS, with a great deal of handiwork done afterward, from brass pins to parts that were cut and then welded using tin. Pieces were glued and sanded in bringing the final machine to fruition. This Enigma is fully functional, but also unique.Their transmission protocol for the device was as follows:“One of the main differences in Enigma is that rotors positions change for each letter (each 1 letter for rotor I, each 26th letter for rotor II…). For instance, AAAAAAA CFRTUIJ,” explains the team. “For a single letter encryption, the operator press a touch on the keyboard: it enables a current travelling through the rotors (cables and pins), being reflected through the reflector and being displayed using lamps.”
“The complexity of the Enigma encryption scheme is increased with the plugboard: it allows the operator to transform each letter in another before the rotors. For decryption, rotors must be replaced in their initial position and the ciphertext will be typed on the Enigma keyboard.”
- Settings, written in a book daily, changed each month in terms of initial position, rotors to be used, plugboard connections, and ring position.
- Operators chose three random letters.
- Rotors and ring positions, with day plugboard connections were set.
- The initial position was encrypted twice and then sent twice as the students worked to doublecheck on the ‘integrity of the transmission.’
- The rotors were placed in the initial position and the writing of the ciphertext began.
“Only six letters are encrypted with the same initial position: frequency analysis was unefficient,” stated the students. “However, position of rotors II and III may not change in 6 letters: it was one breach in the Enigma encryption scheme.”
To find out more about the encryption, functionality, and construction of the 3D printed Enigma, see the students’ design page. Discuss in the Enigma forum at 3DPB.com.
[Source: Hackaday; Pascal Blog]Subscribe to Our Email Newsletter
Stay up-to-date on all the latest news from the 3D printing industry and receive information and offers from third party vendors.
You May Also Like
3D Printing News Briefs, April 13, 2024: Robotics, Orthotics, & Hypersonics
In 3D Printing News Briefs today, we’re focusing first on robotics, as Carnegie Mellon University’s new Robotics Innovation Center will house several community outreach programs, and Ugogo3D is now working...
Rail Giant Alstom Saves $15M with 3D Printing Automation Software 3D Spark
3D Spark has entered into a three-year deal with the rail giant Alstom. Alstom, a transport behemoth with annual revenues of $16 billion, specializes in the manufacture of trains, trams,...
Meltio Expands Global Reach with New Partnerships in the Americas and Europe
Spanish 3D printing manufacturer Meltio has expanded its sales network across the globe. With the addition of three new partners in the United States, Brazil, Argentina, and Italy, Meltio aims...
3D Printing Webinar and Event Roundup: April 7, 2024
Webinars and events in the 3D printing industry are picking back up this week! Sea-Air-Space is coming to Maryland, and SAE International is sponsoring a 3D Systems webinar about 3D...